The existing security model was 'Castle-and-Moat' method. Once inside the network, all resources were accessible,
but this was defenseless against insider threats or administrator account theft.
Woohyun Digital wants to implement the zero trust principle of "Never Trust, Always Verify" across DVR/NVR and security systems to
provide a next-generation security architecture that validates all connections between devices, networks and users in real time
The beginning of security is hardware. Apply hardware-level security technology to
overcome the limitations of software security.
Equipped with Secure Element/TPM: Securely store your device-specific encryption key inside your hardware
chipset to prevent replication and deodorization.
Device ID Authentication: All devices that connect to the network must be identified through a unique digital
certificate to allow the connection.
Security starts the moment the embedded Linux system boots.
Chain of Trust: Validates digital signatures at each boot step leading to the bootloader, kernel, and file system.
If unauthorized firmware modulation is detected, the system immediately blocks the operation.
Anti-Rollback technology: Prevents hacking attempts by forcing downgrading to an older version of firmware
where the vulnerability is found.
Even within the network, barriers between services are established to prevent damage spread.
Service-Level Access Control: Separate and manage each service unit, including video streaming, setting changes,
and firmware updates. Even if a particular service is attacked, the threat does not spread to the entire system.
Role-Based Access Control (RBAC): Grant administrators with minimal access to only essential functions for their work
When transferring data, it performs mutual authentication that 'only the server checks the client as well as 'the client checks the server’.
End-to-End Encryption: Powerfully encrypts all video data segments from cameras to NVR, VMS,
and mobile apps to disable man-in-the-middle attacks.
Continuous Monitoring: Real-time monitoring of device status and traffic patterns even after the connection is established,
blocking sessions immediately in the event of an anomaly
| Item | Traditional security methods (Perimeter) | Woohyun Digital Zero Trust |
|---|---|---|
| Authentication Method | Single authentication based on ID/Password | Multiple Authentication (MFA) |
| Network Access | Allow all resources when entering the network | Allow only verified services/devices to be limited |
| Device Security | Software-based firewall dependence | Hardware & Software based integrity verification |
| Threat Response | Post-invasion response | Real-time monitoring to block out instantly |
| Confidence Range | Trust your internal network to be secure | Don't trust anywhere Inside/Outside |
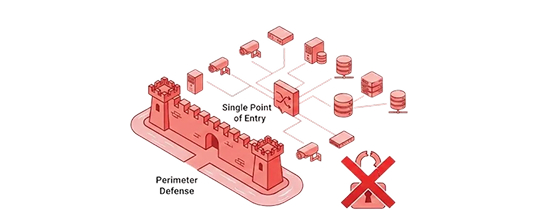
Implicit Trust: Once inside, all access is granted.
Vulnerable to lateral movement.

Explicit Trust: Naver trust, always verify.
Every access is authenticated and authorized.
It proactively meets the globally strengthened cybersecurity regulations of video security equipment, such as the NDAA in the United States
and the Cyber Resilience Act (CRA) in Europe, and is the most reliable technological competitiveness to enter the global market in the future.
Video leaks caused by hacking are fatal to a company's brand value. Woohyun Digital's Zero Trust technology
lowers the possibility of data leakage to near zero, completely protecting your customers' tangible and intangible assets.
Automated device authentication and a centralized permission management system make it easy to maintain
consistent security policies in environments with hundreds or thousands of equipment.
Video security systems are evolving beyond mere surveillance tools into a core infrastructure. Woohyun Digital combines the extreme optimization
capabilities of embedded environments with advanced zero-trust security technology to provide uninterrupted safety under any threat.
